Fake Hacking Screen
Do you want to come off as a computer whiz and skilled hacker? When people witness anything they believe to be hacking, they are frequently impressed because hacking demands a high level of computer understanding. To give the impression that you are hacking, you don’t even need to break the law. All you need to do is use a web browser or the Windows Command Prompt (CMD) to simulate hacking. Continue reading for advice on how to use simulators and simple terminal commands to appear like a hacker.
Things You Should Know
Run intimidating but safe commands that mimic hacking using Terminal on a Mac or Command Prompt (cmd) on Windows.
It is possible to write a batch script on Windows that simulates real-time file downloads and system hacking.
Hacker interfaces that appear realistic in your browser are displayed by websites such as GeekTyper and Hacker Typer.
1 Using Command Prompt or Terminal

- On Windows, you can do so by typing cmd into the Windows search bar and clicking Command Prompt in the search results. Fake Hacking Screen
- On a Mac, click the Launchpad, type terminal, and click Terminal in the search results.
 2 Change the text color. Nothing says “I’m a hacker” more than bright green or blue text on a black background. To change your CMD or Terminal color:
2 Change the text color. Nothing says “I’m a hacker” more than bright green or blue text on a black background. To change your CMD or Terminal color:
- Windows: Type color 0A and press Enter for green text on a black background. You can also type color //? to see a full list of color options.
- Mac: Click the Terminal menu and go to Settings > Profiles. Select the Homebrew profile for a black background with green and blue text.

Use the Command Prompt or Terminal to imitate hacking. There are many commands you can use that look impressive but won’t damage your computer and are not illegal. Fake Hacking Screen
- Windows commands: Type any of the following commands and hit ↵ Enter right after. Type each command in relatively quick succession to make your simulated hacking seem more complex:
- tree
- For a longer version of this command, try tree \. If you get tired of seeing the text scroll by, press Ctrl + C to stop it.
- dir \
- ipconfig /all
- ping -t google.com: The ping command checks to see if a device is reachable on a network, but the common person doesn’t know that). Google is used as an example here, but you can use any website or IP address.
- This command will keep running until you stop it. To stop it, press Ctrl + C.
- tree
- Mac commands: If you have a Mac, you can use the following safe commands to fill your screen with what looks like hacking. Type the following commands into your Terminal and press Return after each:
- top
- ps -ely
- ls -R /
- ping google.com: You can replace google.com with any hostname or IP address. If you want to stop the command, press Ctrl + C.

- Windows commands: Type any of the following commands and hit ↵ Enter right after. Type each command in relatively quick succession to make your simulated hacking seem more complex:
Making a Batch File in Windows


- Paste this code into your Notepad file:
@echo off
color a
title HACK THE PLANET
echo Scan the network? Y/N
PAUSE >nul
arp -a
ping -n 10 8.8.4.4
echo Secure connection available. Hack into computer and download all files? Y/N
PAUSE >nul
echo Hacking into system… please wait…
timeout /t 5 >nul
echo Successfully connected to system. Downloading all files… this may take a while.
timeout /t 5 >nul
dir /s “C:\Program Files”
echo All files downloaded and decrypted.
echo Cover your tracks? Y/N
PAUSE >nul
echo Deleting hack history…
timeout /t 5 >nul
cls
echo Press X to disconnect from the hacked system.
PAUSE >nul

- Saving the file to your desktop makes it easiest to run.

- If you installed Windows on a drive other than your C drive, you might get an error when you run this script. If so, replace the “C” in “C:\Program Files” with the proper drive letter. You can also change this path to any folder you want, such as a fake folder that contain files with names like “Passwords” or “Private Information.” Fake Hacking Screen
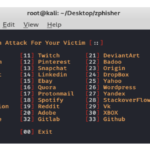
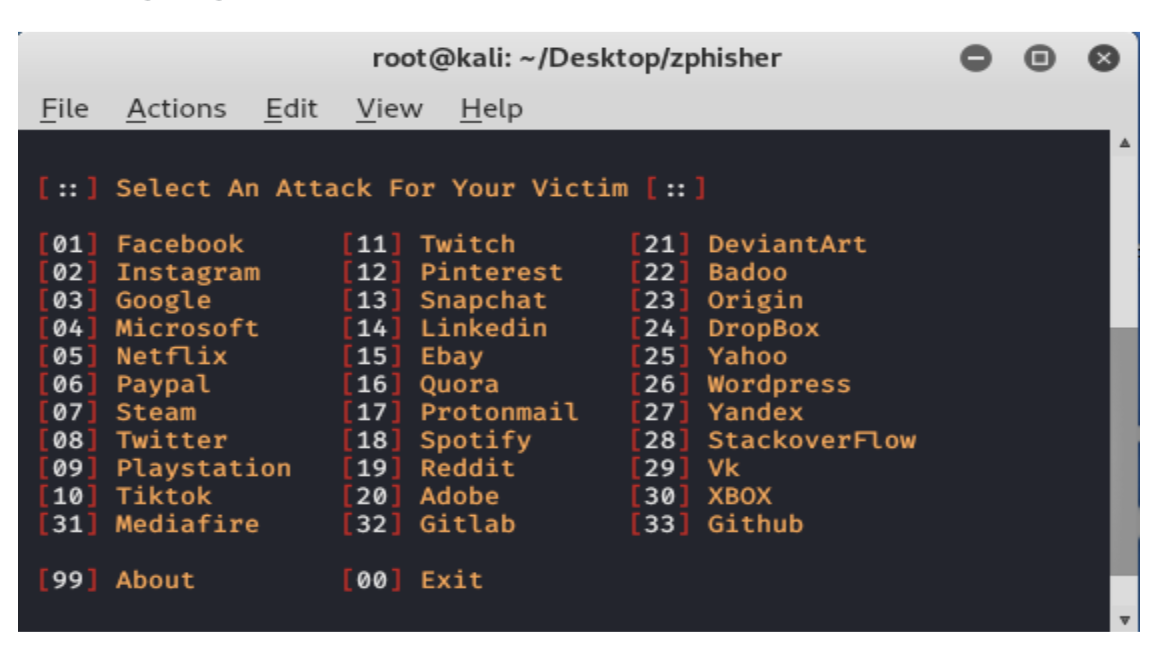
Using Websites

Geektyper. Visit https://www.geektyper.com for a great simulated hacker experience. This site utilizes perhaps the most realistic hack-mimicking simulator. After arriving at the site homepage, choose a theme, then proceed to type to prompt hacker-like text. You can even click folders to run elaborate, albeit fake, processes. Fake Hacking Screen
- Choose a theme, then move between the keystroke-generated fake hacker text and processes by clicking folders and windows.



- Try different arrangements of open windows, or you can leave a few open in the background to make it look like you’re a master hacker. Fake Hacking Screen
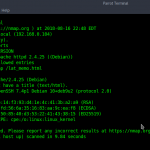
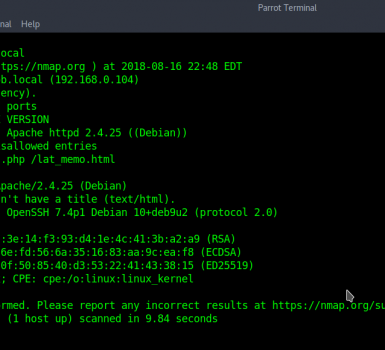
Using Linux (Ubuntu & Debian)