Wapiti is a vulnerability assessment framework that performs black box security auditing of the web applications. The vulnerabilities that can be assessed with Wapiti include database injections, Local File Inclusion (LFI), Remote File Inclusion (RFI), command execution, CRLF injection, Server Side Request Forgery (SSRF), XML External Entity (XXE) injection, Shellshock bugs, .htaccess attacks, and source code disclosure vulnerabilities. The database injection includes SQL, XPATH, PHP, ASP, and JSP injection attacks. Command execution attack analysis includes detection of eval(), system(), and pastru() vulnerabilities. Wapiti makes use of the pre-installed modules to perform these assessments.
The web-application vulnerability scanner
Wapiti allows you to audit the security of your websites or web applications.
It performs “black-box” scans (it does not study the source code) of the web application by crawling the webpages of the deployed webapp, looking for scripts and forms where it can inject data.
Once it gets the list of URLs, forms and their inputs, Wapiti acts like a fuzzer, injecting payloads to see if a script is vulnerable.
What’s new in Wapiti 3.0.9 ? Take a look here.
Wapiti modules cover:
- SQL Injections (Error based, boolean based, time based) and XPath Injections
- Cross Site Scripting (XSS) reflected and permanent
- File disclosure detection (local and remote include, require, fopen, readfile…)
- Command Execution detection (eval(), system(), passtru()…)
- XXE (Xml eXternal Entity) injection
- CRLF Injection
- Search for potentially dangerous files on the server (thank to the Nikto db)
- Bypass of weak htaccess configurations
- Search for copies (backup) of scripts on the server
- Shellshock
- Folder and file enumeration (DirBuster like)
- Server Side Request Forgery (through use of an external Wapiti website)
- Open Redirects
- Detection of uncommon HTTP methods (like PUT)
- Basic CSP Evaluator
- Brute Force login form (using a dictionary list)
- Checking HTTP security headers
- Checking cookie security flags (secure and httponly flags)
- Cross Site Request Forgery (CSRF) basic detection
- Fingerprinting of web applications using the Wappalyzer database
- Enumeration of WordPress and Drupal modules
- Detection of subdomain takeovers vulnerabilities
- Log4Shell vulnerability detection (CVE-2021-44228)
Wapiti supports both GET and POST HTTP methods for attacks.
It also supports multipart forms and can inject payloads in filenames (upload).
Warnings are raised when an anomaly is found (for example 500 errors and timeouts)
Wapiti is able to make the difference between permanent and reflected XSS vulnerabilities.
General features :
- Generates vulnerability reports in various formats (HTML, XML, JSON, TXT, CSV)
- Can suspend and resume a scan or an attack (session mechanism using sqlite3 databases)
- Can give you colors in the terminal to highlight vulnerabilities
- Different levels of verbosity
- Fast and easy way to activate/deactivate attack modules
- Adding a payload can be as easy as adding a line to a text file
- Configurable number of concurrent tasks to perform HTTP requests
Browsing features
- Support HTTP, HTTPS and SOCKS5 proxies
- Authentication via several methods : Basic, Digest, NTLM or GET/POST on login forms
- Ability to restrain the scope of the scan (domain, folder, page, url)
- Automatic removal of one are more parameters in URLs
- Multiple safeguards against scan endless-loops (for example, limit of values for a parameter)
- Possibility to set the first URLs to explore (even if not in scope)
- Can exclude some URLs of the scan and attacks (eg: logout URL)
- Import cookies from your Chrome or Firefox browser or using the wapiti-getcookie tool
- Can activate / deactivate SSL certificates verification
- Extract URLs from Flash SWF files
- Try to extract URLs from javascript (very basic JS interpreter)
- HTML5 aware (understand recent HTML tags)
- Several options to control the crawler behavior and limits.
- Skipping some parameter names during attack.
- Setting a maximum time for the scan process.
- Adding some custom HTTP headers or setting a custom User-Agent.
pip install wapiti3
Usage
██╗ ██╗ █████╗ ██████╗ ██╗████████╗██╗██████╗
██║ ██║██╔══██╗██╔══██╗██║╚══██╔══╝██║╚════██╗
██║ █╗ ██║███████║██████╔╝██║ ██║ ██║ █████╔╝
██║███╗██║██╔══██║██╔═══╝ ██║ ██║ ██║ ╚═══██╗
╚███╔███╔╝██║ ██║██║ ██║ ██║ ██║██████╔╝
╚══╝╚══╝ ╚═╝ ╚═╝╚═╝ ╚═╝ ╚═╝ ╚═╝╚═════╝
Wapiti-3.0.9 (wapiti.sourceforge.io)
usage: wapiti [-h] [-u URL] [--scope {page,folder,domain,url,punk}]
[-m MODULES_LIST] [--list-modules] [--update] [-l LEVEL]
[-p PROXY_URL] [--tor] [-a CREDENTIALS]
[--auth-type {basic,digest,ntlm,post}] [-c COOKIE_FILE]
[--drop-set-cookie] [--skip-crawl] [--resume-crawl]
[--flush-attacks] [--flush-session] [--store-session PATH]
[--store-config PATH] [-s URL] [-x URL] [-r PARAMETER]
[--skip PARAMETER] [-d DEPTH] [--max-links-per-page MAX]
[--max-files-per-dir MAX] [--max-scan-time SECONDS]
[--max-attack-time SECONDS] [--max-parameters MAX] [-S FORCE]
[--tasks tasks] [-t SECONDS] [-H HEADER] [-A AGENT]
[--verify-ssl {0,1}] [--color] [-v LEVEL] [-f FORMAT]
[-o OUTPUT_PATH] [--log OUTPUT_PATH]
[--external-endpoint EXTERNAL_ENDPOINT_URL]
[--internal-endpoint INTERNAL_ENDPOINT_URL]
[--dns-endpoint DNS_ENDPOINT_DOMAIN] [--endpoint ENDPOINT_URL]
[--no-bugreport] [--version]
wapiti: error: one of the arguments -u/--url --list-modules --update is required
Shortest way (with default options) to launch a Wapiti scan :
wapiti -u http://target/
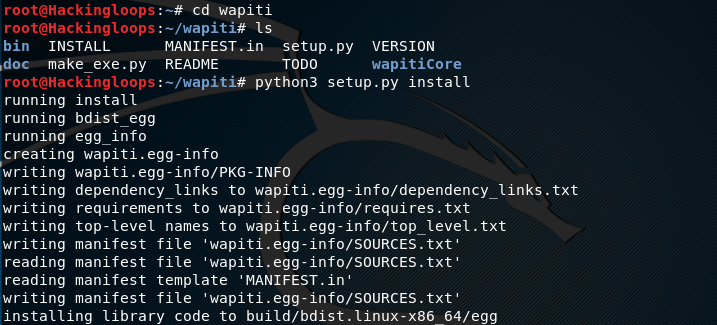
Wapiti Installation
Wapiti is a Python based framework. Clone Wapiti using the following Github path.
git clone https://github.com/IFGHou/wapiti
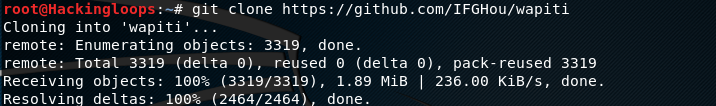
Navigate to the wapiti directory to install the framework using the following commands.
cd wapiti python3 setup.py install
Wapiti Working
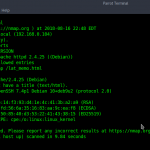
The framework can be launched by running the wapiti executable from bin folder in Wapiti directory. The help command loads all the mandatory and optional parameters of Wapiti.
python3 wapiti -h
The following basic command executes Wapiti framework to scan vulnerabilities in target web application.
python3 wapiti –u <target web application>
Let’s assume a web application (testphp.vunweb.com). The following command loads all Wapiti modules to scan the application for the aforesaid vulnerabilities.
python3 wapiti –u http://testphp.vulbweb.com
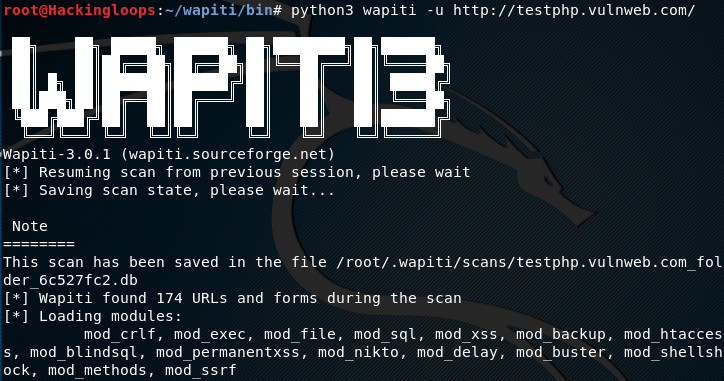
Wapiti finds all the available links on the target web application and runs each module one by one against each file (link). If any file (link) is found vulnerable, Wapiti mentions it in Command Line Interface (CLI) along with the attack path and potential injection parameters.
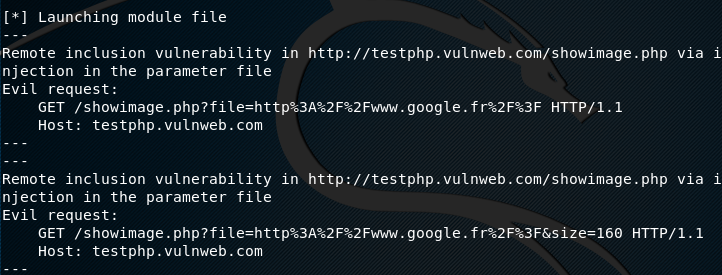
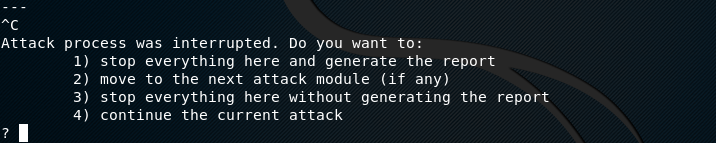
Since Wapiti basic command loads all the modules, the process can take some time to scan web applications with too many directories and pages. The CTRL+C command halts the current scan process with few options, such as skipping the active module and executing the next, generating report without performing further analysis, and stopping the whole scanning process without generating any reports.
Besides launching all modules, Wapiti allows using a specific module. The –lists-modules argument lists all the available modules in Wapiti framework.
Python3 wapiti --list-modules

The –m parameter in the following format executes desired module for specific vulnerabilities assessment.
python3 wapiti –u <target web application> -m <module name>
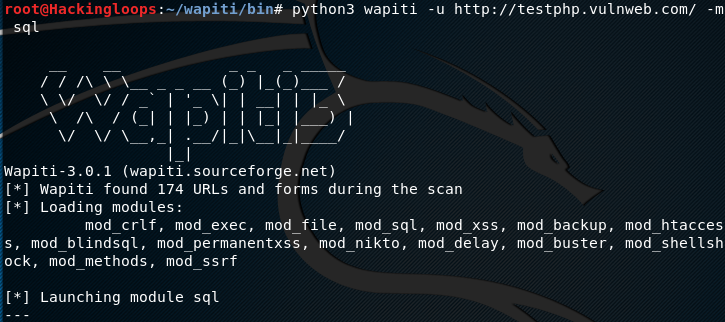
For instance, we can limit the vulnerability search scope to SQL injections by using the sql module in the following format.
python3 wapiti –u http://testphp.vulnweb.com –m sql
The above command loads all the modules, however executes only sql module to find out SQL related vulnerabilities in the target web application.
The module goes through each directory and page to find out the SQL vulnerabilities. We can define depth level to limit the scanning process to desired number of links or files. The –max-links-per-page argument is used to define the maximum links to be scanned one each page of the target web application. Similarly, –max-files-per-dir argument is used to define maximum number of files per directory. Wapiti supports many other arguments that can be used along with the search command. All these options can be explored in the help section. Besides displaying individual findings in CLI, Wapiti generates a detailed report of detected vulnerabilities in the root directory. The report is in HTML format that can be viewed in preferred web browser.

Conclusion
Wapiti is an automated way of searching top level web application vulnerabilities. The framework does not rely on the provided url path. Rather, it scans all the directories and pages in the target to find out the potential vulnerabilities.