The red and blue team security are much more than just Halo references and troop techniques. In fact, these teams play a vital role in defending against advanced cyber attacks that threaten business communications, sensitive customer data or trade secrets.
Red teams are aggressive security professionals who specialize in attacking systems and breaching defenses. Blue Teams are defensive security professionals responsible for maintaining internal network security against all cyber attacks and threats. Red teams simulate attacks against blue teams to test the effectiveness of protecting the network. These Red and Blue team exercises provide a holistic security solution ensuring robust security keeping in view the emerging threats.
What Is A Red Team?
A red team consists of security professionals who act as adversaries to circumvent cyber security controls. Red teams often have independent ethical hackers who evaluate system security in an objective manner.

They use all available techniques (discussed below) to detect vulnerabilities in people, processes and technology to gain unauthorized access to assets. As a result of these spurious attacks, red teams make recommendations and plans on how to strengthen the organization’s security position.
How Does A Red Team Work?
You might be surprised to learn (like I was) that red teams spend more time planning an attack then they attack. In fact, the Red Team deploys several methods to gain access to the network.
Social engineering attacks, for example, rely on reconnaissance and research to deliver targeted spear phishing campaigns. Similarly, before performing penetration testing, packet sniffers and protocol analyzers are used to scan the network and collect as much information as possible about the system.
Typical information gathered during this phase includes:
- Uncovering operating systems in use (Windows, macOS, or Linux).
- Identifying the make and model of networking equipment (servers, firewalls, switches, routers, access points, computers, etc.).
- Understanding physical controls (doors, locks, cameras, security personnel).
- Learning what ports are open/closed on a firewall to allow/block specific traffic.
- Creating a map of the network to determine what hosts are running what services along with where traffic is being sent.
Once the red team has a more complete understanding of the system, they develop an action plan designed to target specific vulnerabilities to the information gathered above.
For example, a Red Team member may discover that a server is running Microsoft Windows Server 2016 R2 (a server operating system) and that the default domain policies may still be in use.
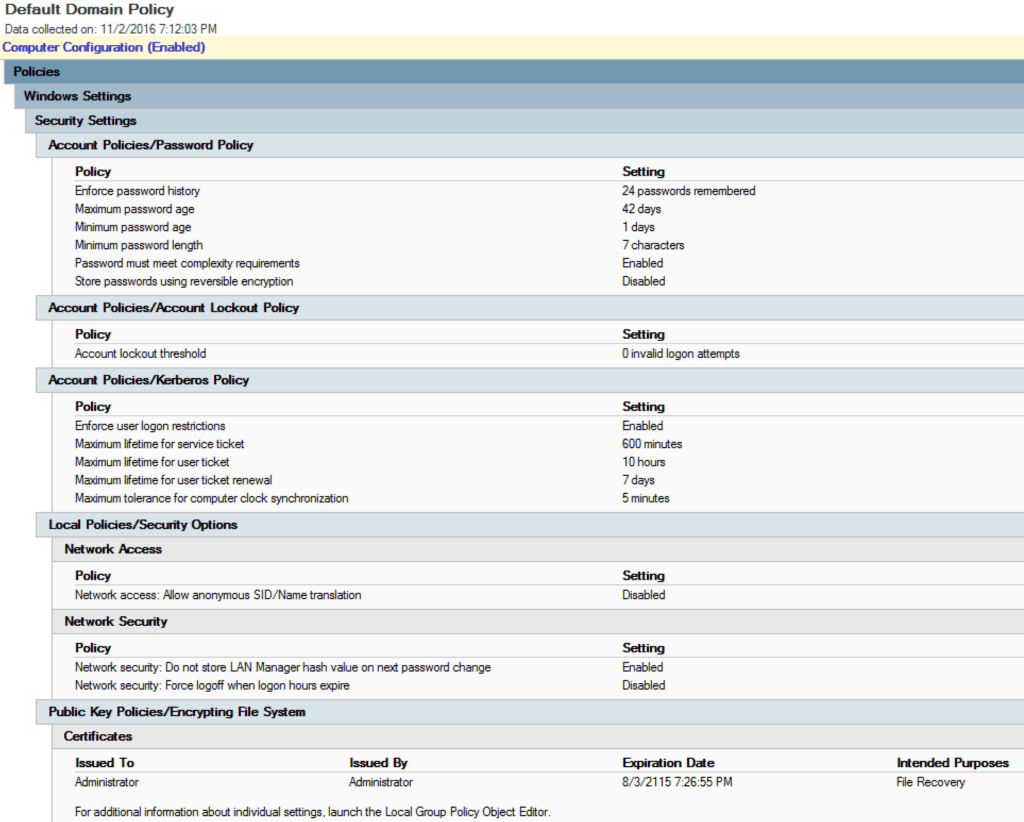
Microsoft “ships” its software in its default state, which leaves it up to network administrators to update policies, which Microsoft recommends that you do so as soon as possible to harden network security. If still set to its default state, an attacker could be working to compromise the security measures that are comfortably in place.
Once vulnerabilities are identified, a red team tries to exploit those vulnerabilities to gain access to your network. Once an attacker is in your system the typical course of action is to use privilege escalation techniques, whereby the attacker attempts to steal the credentials of an administrator who has more/full access to the highest level of critical information Is.
The Tiger Team
In the early days of network security, a Tiger team performed many of the same tasks as a Red team. The term has evolved over the years to now refer to Tiger teams as a specialized and highly specialized group that are hired to take on a particular challenge against an organization’s security posture.
Examples Of Red Team Exercises
The Red Team uses a variety of methods and tools to exploit vulnerabilities and vulnerabilities in the network. It is important to note that Red Teams will use any means necessary, pursuant to the Terms of Engagement, to break into your system. Depending on the vulnerability they may deploy malware to infect hosts or even bypass physical security controls by cloning access cards.
Examples of red team exercises include:
- Penetration testing, also known as ethical hacking, is where the tester tries to gain access to a system, often using software tools. For example, ‘John the Ripper’ is a password-cracking program. It can detect what type of encryption is used, and try to bypass it.
- Social engineering is where the Red Team attempts to persuade or trick members of staff into disclosing their credentials or allowing access to a restricted area.
- Phishing entails sending apparently-authentic emails that entice staff members to take certain actions, such as logging into the hacker’s website and entering credentials.
- Intercepting communication software tools such as packet sniffers and protocol analyzers can be used to map a network, or read messages sent in clear text. The purpose of these tools is to gain information on the system. For example, if an attacker knows a server is running on a Microsoft operating system then they would focus their attacks to exploit Microsoft vulnerabilities.
- Card cloning of an employee’s security card to grant access into unrestricted areas, such as a server room.
What Is A Blue Team?
A blue team consists of security professionals who have an inside view of the organization. Their job is to protect the important assets of the organization from any kind of danger.

They are well versed with the business objectives and security strategy of the organization. Therefore, their job is to fortify the walls of the palace so that no intruder can compromise the defence.
Blue team definition:
During cyber security testing activities, blue teams evaluate organizational security environments and protect these environments from red teams. These red teams play the role of attackers by identifying security vulnerabilities and launching attacks in a controlled environment. The two teams combine to help uncover the true state of an organization’s security.
The idea that you can better understand your defense by attacking in a controlled environment is a long-established military doctrine. This idea is commonly expressed in the practice of “red teaming”, where an external group of independent actors test a target organization’s systems or security to identify existing vulnerabilities.
In the world of information security, the practice of red teaming is now well established. Red teams, who act as “ethical hackers”, systematically study an organization’s structure and security and then launch attacks to exploit any vulnerabilities.
Yet red teams are only part of the equation. The “blue team” on the other hand – security professionals tasked with protecting an organization’s systems and assets against both real and fake attacks.
How Does A Blue Team Work?
The Blue team first collects the data, documents exactly what needs to be protected and conducts risk assessments. They then strengthen access to the system in a number of ways, including introducing strong password policies and educating employees to ensure they understand and follow security procedures.
Monitoring devices are often installed, allowing information about access to the system to be logged and checked for abnormal activity. Blue teams will conduct routine checks on the system, for example, DNS audits, internal or external network vulnerability scans, and capture sample network traffic for analysis.
Blue teams have to set up security measures around key assets of an organization. They begin their defensive plan by identifying important assets, documenting the importance of these assets to the business and what effect the absence of these assets has.
Blue teams then conduct a risk assessment against each asset by identifying threats and vulnerabilities that exploit these threats. By evaluating and prioritizing risks, the Blue team develops an action plan to implement controls that can reduce the impact or likelihood of hazards occurring against the asset.
The involvement of senior management is important at this stage as only they can decide whether to accept the risk or apply mitigation controls against it. The selection of controls is often based on a cost-benefit analysis to ensure that security controls provide maximum value to the business.
For example, a blue team may identify that a company’s network is vulnerable to a DDoS (Distributed Denial of Service) attack. This attack reduces network availability for legitimate users by sending incomplete traffic requests to a server. Each of these requests requires resources to process, which is why the attack severely paralyzes a network.
In case of danger, the team calculates the damage. Based on a cost-benefit analysis and aligning with business objectives, a blue team will consider setting up an intrusion detection and prevention system to reduce the risk of DDoS attacks.
Examples Of Blue Team Exercises
Blue teams use a variety of methods and tools as countermeasures to protect a network from cyber attacks. Depending on the situation a blue team may determine that additional firewalls need to be installed to block access to the internal network. Or, the risk of social engineering attacks is so significant that it warrants the cost of implementing security awareness training company-wide.
Examples of blue team exercises include:
- Performing DNS audits (domain name server) to prevent phishing attacks, avoid stale DNS issues, avoid downtime from DNS record deletions, and prevent/reduce DNS and web attacks.
- Conducting digital footprint analysis to tracks users’ activity and identify any known signatures that might indicate a breach of security.
- Installing endpoint security software on external devices such as laptops and smartphones.
- Ensuring firewall access controls are properly configured and that antivirus software are kept up to date
- Deploying IDS and IPS software as a detective and preventive security control.
- Implementing SIEM solutions to log and ingest network activity.
- Analyzing logs and memory to pick up unusual activity on the system, and identify and pinpoint an attack.
- Segregating networks and ensure they are configured correctly.
- Using vulnerability scanning software on a regular basis.
- Securing systems by using antivirus or anti-malware software.
- Embedding security in processes.
What Are The Benefits Of Red And Blue Teams?
Implementing a red and blue team strategy allows an organization to benefit from two completely different perspectives and skills. It also brings a certain amount of competition to the task, which encourages high performance of both teams.
The Red Team is valuable in that it identifies vulnerabilities, but it can only uncover the current state of the system. Blue Team, on the other hand, is valuable in that it provides long-term security by ensuring security and continuously monitoring the system.
The major advantage, however, is the continuous improvement of the security situation of the organization by finding the shortcomings and then filling those gaps with appropriate controls.
How Do Red And Blue Teams Work Together?
Communication between the two teams is the most important factor in successful red and blue team exercises.
The blue team should stay up to date on the new technologies for improving security and should share these findings with the red team. Likewise, the red team should always be aware of new threats and penetration techniques used by hackers and advise the blue team on prevention techniques.
Depending on the goal of your test will depend on whether or not the red team informs the blue team of a planned test. For example, if the goal is to simulate a real response scenario to a “legitimate” threat, then you wouldn’t want to tell the blue team about the test.
The caveat is that someone in management should be aware of the test, typically the blue team lead. This ensures the response scenario is still tested, but with tighter control when/if the situation is escalated.
When the test is complete both teams gather information and report on their findings. The red team advises the blue team if they manage to penetrate defenses, and provide advice on how to block similar attempts in a real scenario. Likewise, the blue team should let the red team know whether or not their monitoring procedures picked up an attempted attack.
Both teams should then work together to plan, develop, and implement stronger security controls as needed.
RED TEAM VS. BLUE TEAM EXERCISES: HOW THEY WORK
Blue teams conduct operational network security evaluations and provide relevant mitigation tools and techniques for organizations seeking to gauge their defenses or prepare for red team attacks.
Blue teams are often composed of the security personnel within an organization, or that organization may select certain team members to create a dedicated blue team within the department. Blue teams may also be independent consultants hired for specific engagements who use their expertise to help audit the state of an organization’s defenses.
When an organization schedules red team vs. blue team exercises, red teams may attempt a range of techniques to launch a successful attack. These techniques are very open-ended and not always confined to the digital realm.
Red team attacks may include scenarios such as a red team member posing as a vendor to infiltrate the target organization. This person may slip into the room undetected and quietly install malware, gaining network access.
Before getting started, red teams typically engage in digital reconnaissance to evaluate organizational defenses, then deploy various sophisticated attack techniques to compromise the target’s security while avoiding detection.
Blue teams are tasked with rebuffing these attacks and exposing red team activity. This often begins with a detailed risk assessment of the organization’s current security posture. Blue teams then may deploy a combination of human intelligence activity and technical tools to detect and rebuff red team incursions.
Ultimately, a blue team is expected to analyze log data, perform traffic analysis, execute audits, perform digital footprint and risk intelligence analysis, and take other similar steps to prevent any breaches — and then rectify any uncovered vulnerabilities.
THE VALUE OF BLUE TEAM TESTING
A skilled cyber security blue team can play a critical role in helping to develop a comprehensive plan for organizational defense using the latest tools and techniques — a “blue team security stack,” in other words. Often, it’s best to think of them as the most active contingent of a security team.
Not all security team personnel specialize in tasks that are considered to be high-level or relevant enough for testing. Blue teams are focused on high-level threats and are dedicated to continuous improvement in detection and response techniques.
To succeed, blue teams must be rigorously thorough; after all, red teams can launch 99 unsuccessful attacks and still win on the 100th attempt. Blue teams must be right all the time. In addition to attention to detail, blue teams must also think creatively and have the ability to adapt on the fly. This is because many of the most effective red teamers (and black hat hackers) are remarkably adept at formulating novel and hard-to-predict attack techniques.
By evaluating the work of both red and blue teams, organizations can develop a holistic picture of the state of their security — and make any changes that may be required to ensure a robust overall defense.
What Is A Purple Team?
While red teams and blue teams share common goals, they’re often not politically aligned. For example, red teams who report on vulnerabilities are praised for a job well done. Therefore, they’re not incentivized to help the blue team strengthen their security by sharing information on how they bypassed their security.
There’s also no point in “winning” red team tests if you’re not sharing that information with the blue team. Remember, the main purpose of red and blue team exercises is to strengthen the overall security posture of the organization.
That’s where the concept of a purple team comes into place. A purple team isn’t necessarily a stand alone team, although it could be. The goal of a purple team is to bring both red and blue teams together while encouraging them to work as a team to share insights and create a strong feedback loop.
Management should ensure that the red and blue teams work together and keep each other informed. Enhanced cooperation between both teams through proper resource sharing, reporting and knowledge share is essential for the continual improvement of the security program.