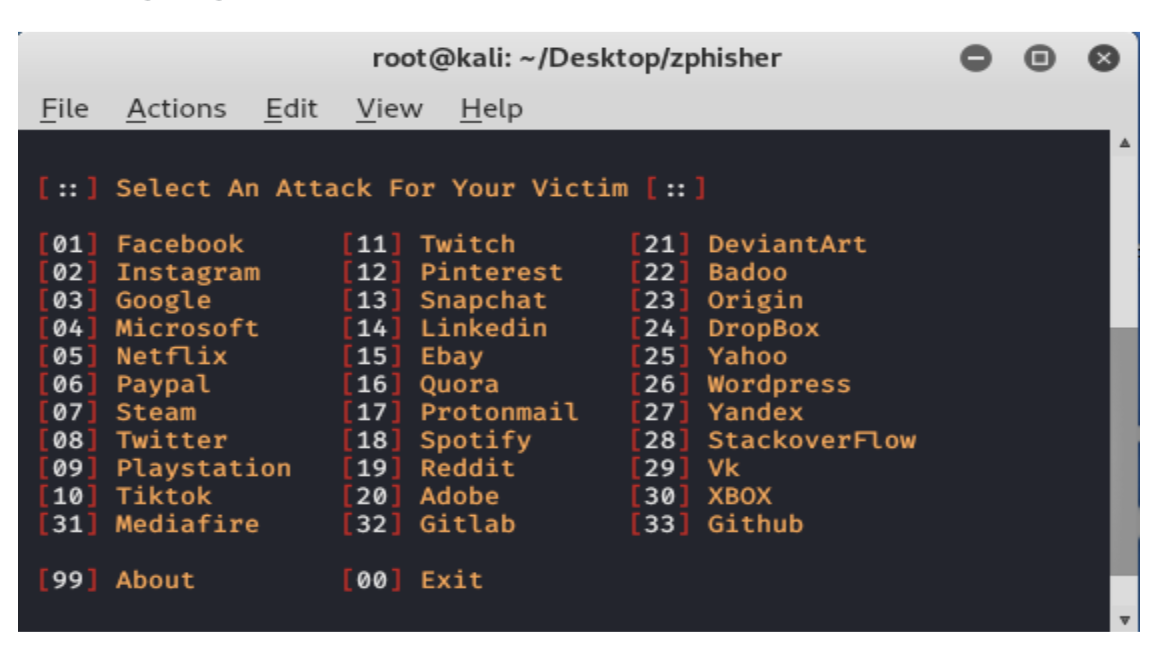
Nmap is the most well-known scanning tool used by penetration testers. In this article, we will look at some of the main features of Nmap along with some useful commands.
What is Nmap?
Nmap is short for Network Mapper. It is an open-source Linux command-line tool used to scan IP addresses and ports in a network and locate installed applications.
Nmap allows network administrators to find out what devices are running on their network, discover open ports and services, and detect vulnerabilities.
Gordon Lyons (pseudonym Fyodor) wrote Nmap as a tool to help people easily map an entire network and find its open ports and services.
Namp has become extremely popular, having appeared in films such as The Matrix and the popular series Mr. Robot.
Why use Nmap?
There are several reasons why security professionals prefer Nmap over other scanning tools.
First, nmap helps you quickly map networks without sophisticated commands or configurations. It also supports simple commands (for example, to check if a host is up) and complex scripting via the Nmap scripting engine.
Other features of Nmap include:
- Ability to quickly recognize all the devices including servers, routers, switches, mobile devices, etc on single or multiple networks.
- Helps identify services running on a system including web servers, DNS servers, and other common applications. Nmap can also detect application versions with reasonable accuracy to help detect existing vulnerabilities.
- Nmap can find information about the operating system running on devices. It can provide detailed information like OS versions, making it easier to plan additional approaches during penetration testing.
- During security auditing and vulnerability scanning, you can use Nmap to attack systems using existing scripts from the Nmap Scripting Engine.
- Nmap has a graphical user interface called Zenmap. It helps you develop visual mappings of a network for better usability and reporting.
Commands
Let’s look at some Nmap commands. If you don’t have Nmap installed, you can get it from here.
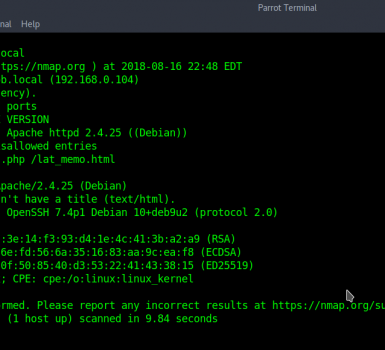
Basic scans
Scanning the list of active devices on a network is the first step in network mapping. There are two types of scans you can use for that:
- Ping scan — Scans the list of devices up and running on a given subnet.
> nmap -sp 192.168.1.1/24- Scan a single host — Scans a single host for 1000 well-known ports. These ports are the ones used by popular services like SQL, SNTP, apache, and others.
> nmap scanme.nmap.org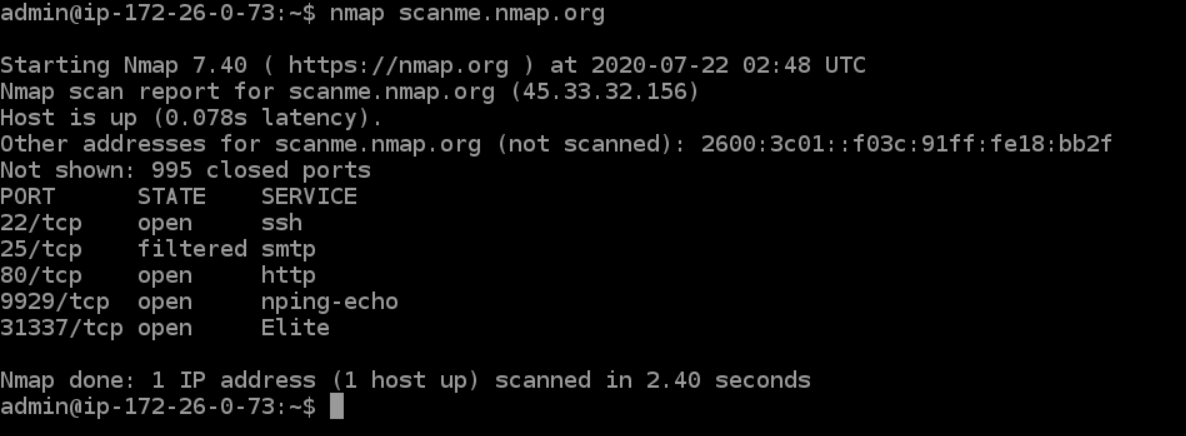
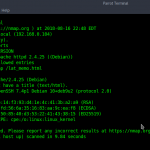
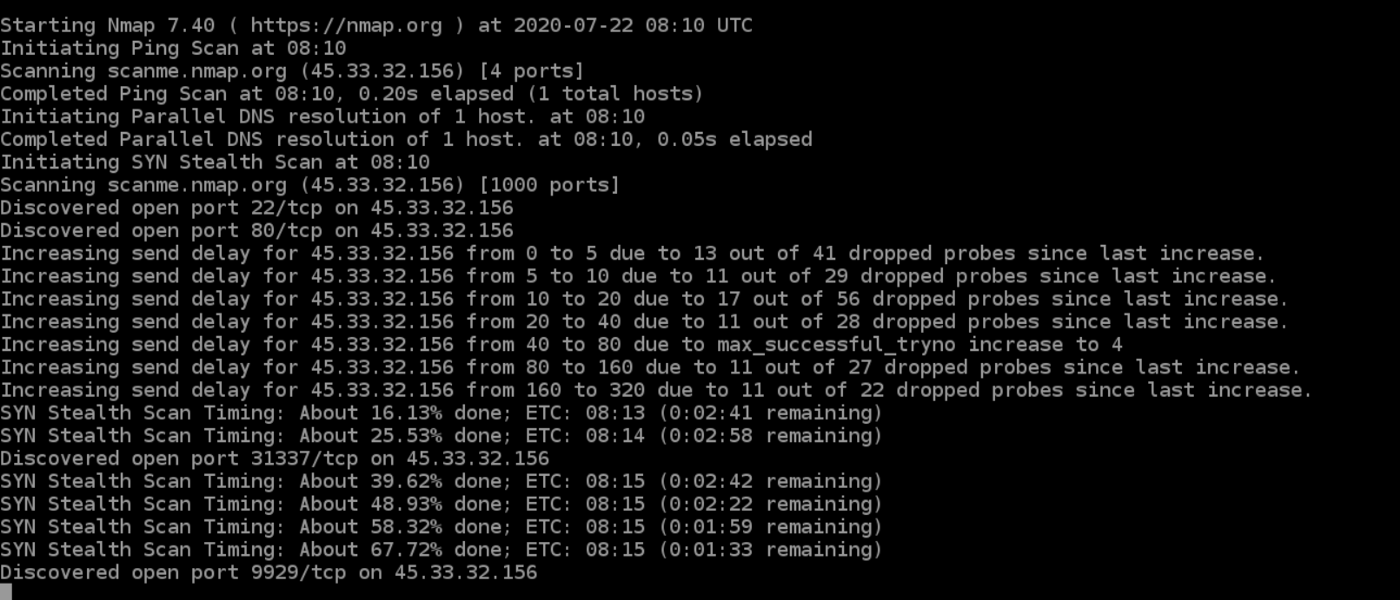
Stealth scan
Stealth scanning is performed by sending an SYN packet and analyzing the response. If SYN/ACK is received, it means the port is open, and you can open a TCP connection.
However, a stealth scan never completes the 3-way handshake, which makes it hard for the target to determine the scanning system.
> nmap -sS scanme.nmap.orgYou can use the ‘-sS’ command to perform a stealth scan. Remember, stealth scanning is slower and not as aggressive as the other types of scanning, so you might have to wait a while to get a response.
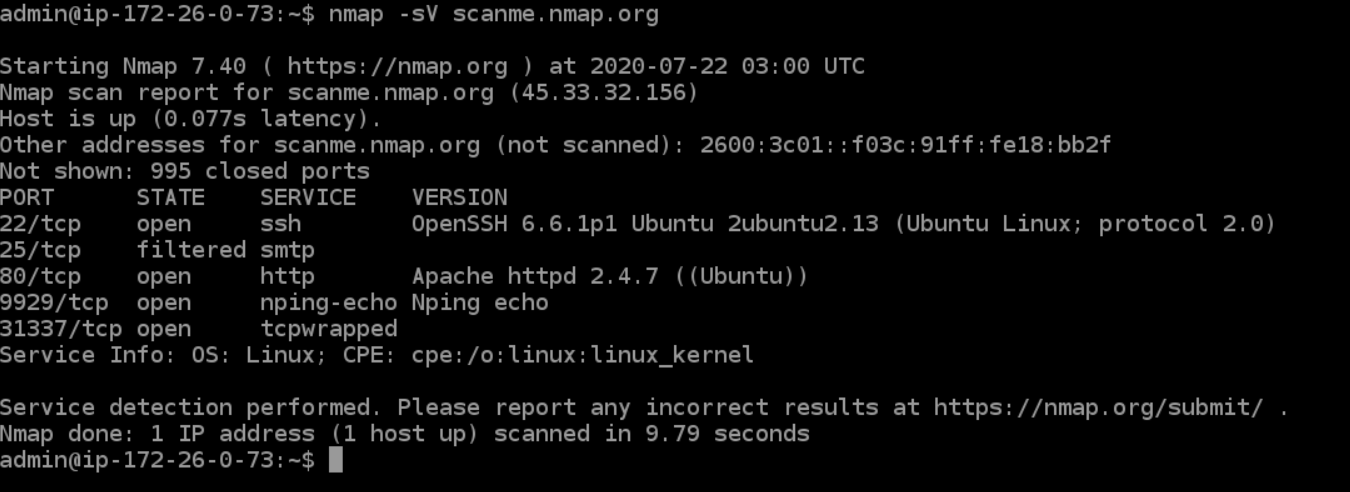
Version scanning
Finding application versions is a crucial part in penetration testing.
It makes your life easier since you can find an existing vulnerability from the Common Vulnerabilities and Exploits (CVE) database for a particular version of the service. You can then use it to attack a machine using an exploitation tool like Metasploit.
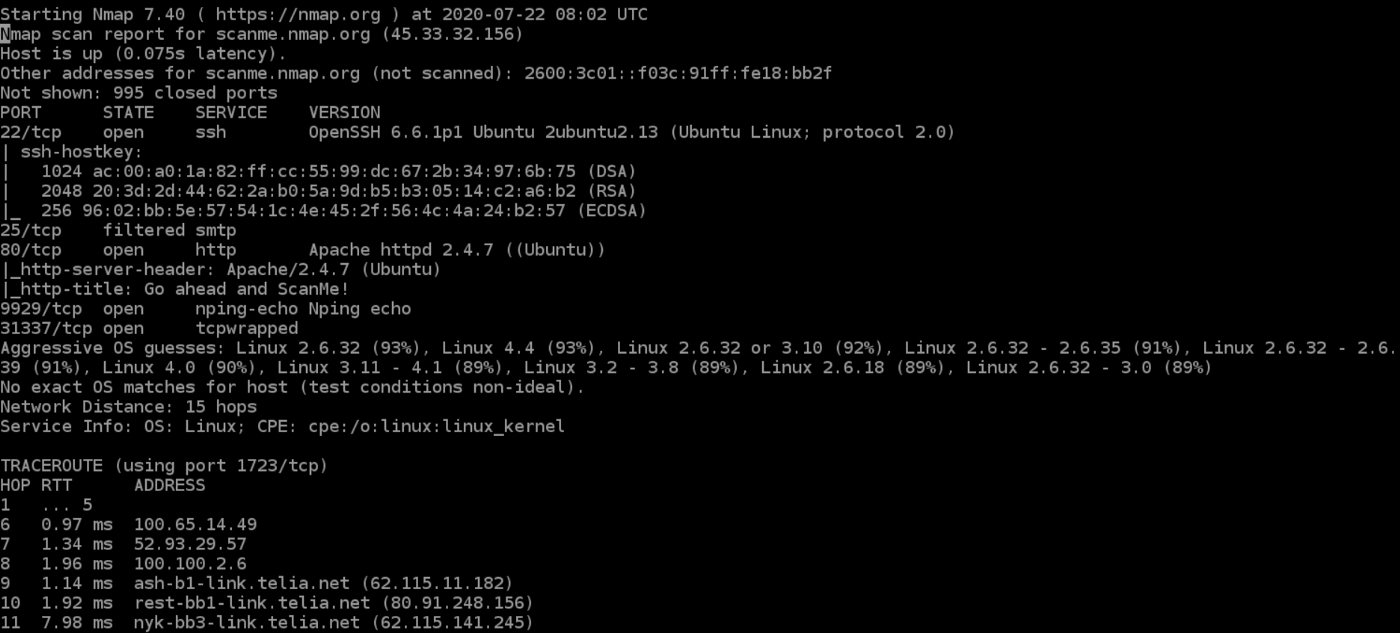
> nmap -sV scanme.nmap.orgTo do a version scan, use the ‘-sV’ command. Nmap will provide a list of services with its versions. Do keep in mind that version scans are not always 100% accurate, but it does take you one step closer to successfully getting into a system.
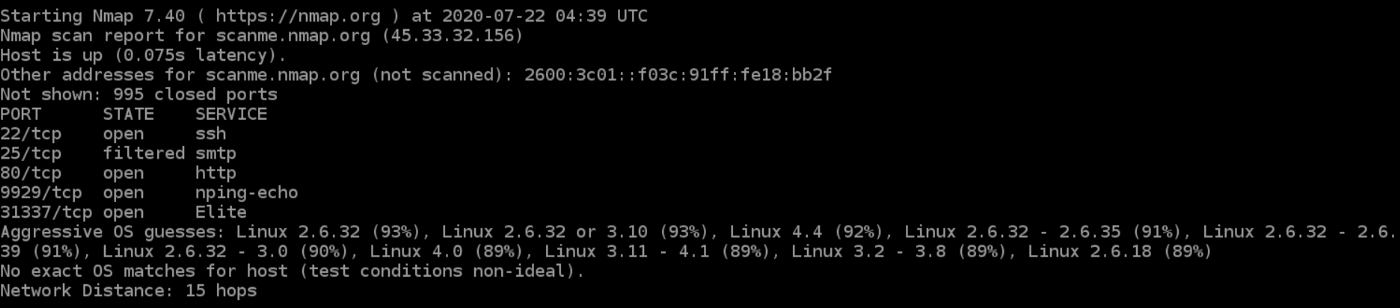
OS Scanning
In addition to the services and their versions, Nmap can provide information about the underlying operating system using TCP/IP fingerprinting. Nmap will also try to find the system uptime during an OS scan.
> nmap -sV scanme.nmap.orgYou can use the additional flags like osscan-limit to limit the search to a few expected targets. Nmap will display the confidence percentage for each OS guess.
Again, OS detection is not always accurate, but it goes a long way towards helping a pen tester get closer to their target.
Aggressive Scanning
Nmap has an aggressive mode that enables OS detection, version detection, script scanning, and traceroute. You can use the -A argument to perform an aggressive scan.
> nmap -A scanme.nmap.orgAggressive scans provide far better information than regular scans. However, an aggressive scan also sends out more probes, and it is more likely to be detected during security audits.
Scanning Multiple Hosts
Nmap has the capability of scanning multiple hosts simultaneously. This feature comes in real handy when you are managing vast network infrastructure.
You can scan multiple hosts through numerous approaches:
- Write all the IP addresses in a single row to scan all of the hosts at the same time.
> nmap 192.164.1.1 192.164.0.2 192.164.0.2- Use the asterisk (*) to scan all of the subnets at once.
> nmap 192.164.1.*- Add commas to separate the addresses endings instead of typing the entire domains.
> nmap 192.164.0.1,2,3,4- Use a hyphen to specify a range of IP addresses
> nmap 192.164.0.0–255Port Scanning
Port scanning is one of the most fundamental features of Nmap. You can scan for ports in several ways.
- Using the -p param to scan for a single port
> nmap -p 973 192.164.0.1- If you specify the type of port, you can scan for information about a particular type of connection, for example for a TCP connection.
> nmap -p T:7777, 973 192.164.0.1- A range of ports can be scanned by separating them with a hyphen.
> nmap -p 76–973 192.164.0.1- You can also use the -top-ports flag to specify the top n ports to scan.
> nmap --top-ports 10 scanme.nmap.orgScanning from a File
If you want to scan a large list of IP addresses, you can do it by importing a file with the list of IP addresses.
> nmap -iL /input_ips.txtThe above command will produce the scan results of all the given domains in the “input_ips.txt” file. Other than simply scanning the IP addresses, you can use additional options and flags as well.
Verbosity and Exporting Scan Results
Penetration testing can last days or even weeks. Exporting Nmap results can be useful to avoid redundant work and to help with creating final reports. Let’s look at some ways to export Nmap scan results.
Verbose Output
> nmap -v scanme.nmap.orgThe verbose output provides additional information about the scan being performed. It is useful to monitor step by step actions Nmap performs on a network, especially if you are an outsider scanning a client’s network.
Normal output
Nmap scans can also be exported to a text file. It will be slightly different from the original command line output, but it will capture all the essential scan results. | nmap commands
> nmap -oN output.txt scanme.nmap.org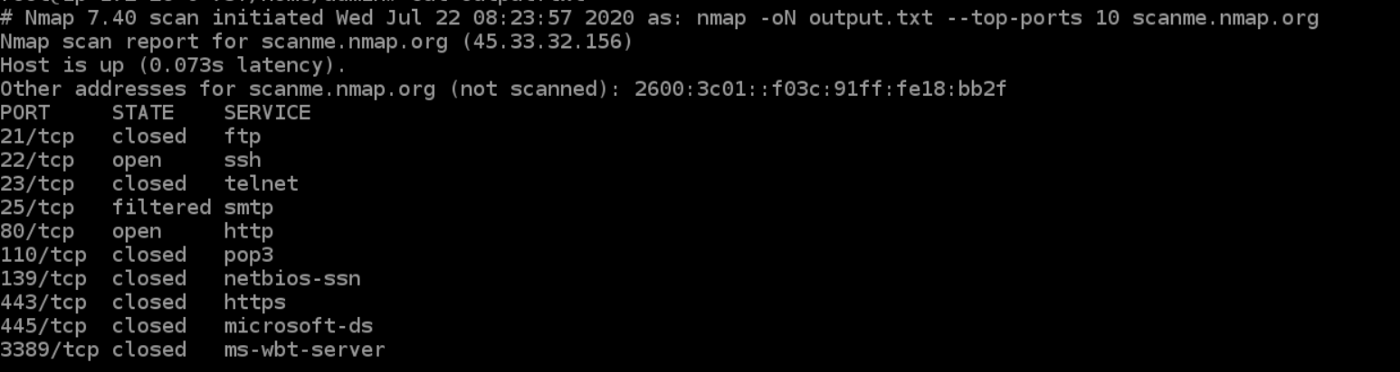
XML output
Nmap scans can also be exported to XML. It is also the preferred file format of most pen-testing tools, making it easily parsable when importing scan results. | nmap commands
> nmap -oX output.xml scanme.nmap.org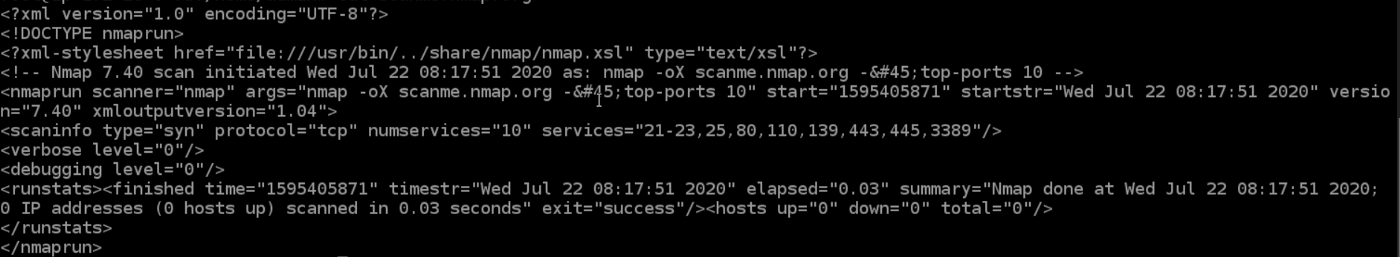
Multiple Formats
You can also export the scan results in all the available formats at once using the -oA command.
> nmap -oA output scanme.nmap.orgThe above command will export the scan result in three files — output.xml, output. Nmap and output.gnmap.
Nmap Help
Nmap has a built-in help command that lists all the flags and options you can use. It is often handy given the number of command-line arguments Nmap comes with.
> nmap -h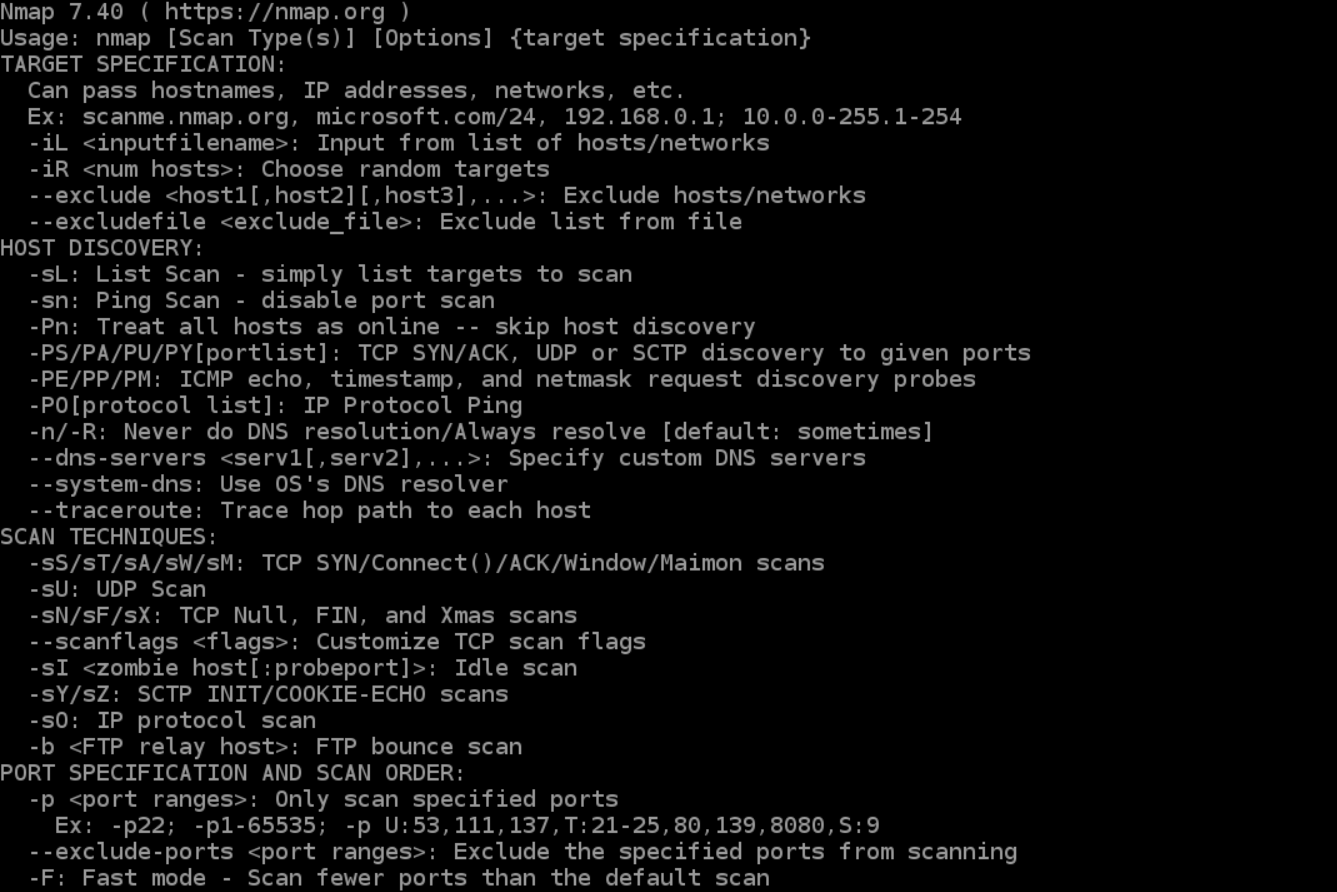
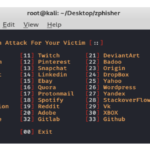
Nmap Scripting Engine
Nmap Scripting Engine (NSE) is an incredibly powerful tool that you can use to write scripts and automate numerous networking features. || nmap commands
You can find plenty of scripts distributed across Nmap, or write your own script based on your requirements. You can even modify existing scripts using the Lua programming language.
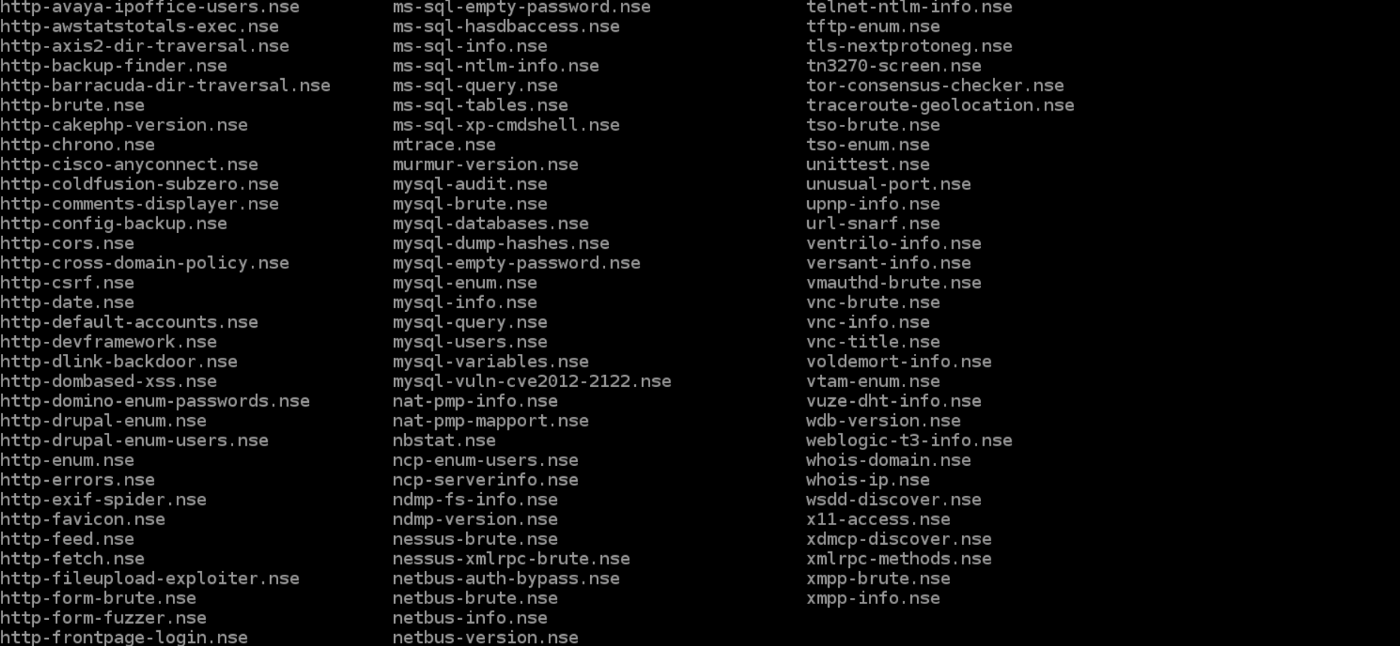
NSE also has attack scripts that are used in attacking the network and various networking protocols.
Going through the scripting engine in-depth would be out-of-scope for this article, so here is more information about the Nmap scripting engine.
Zenmap
Zenmap is a graphical user interface for Nmap. It is a free and open-source software that helps you get up and running with Nmap.
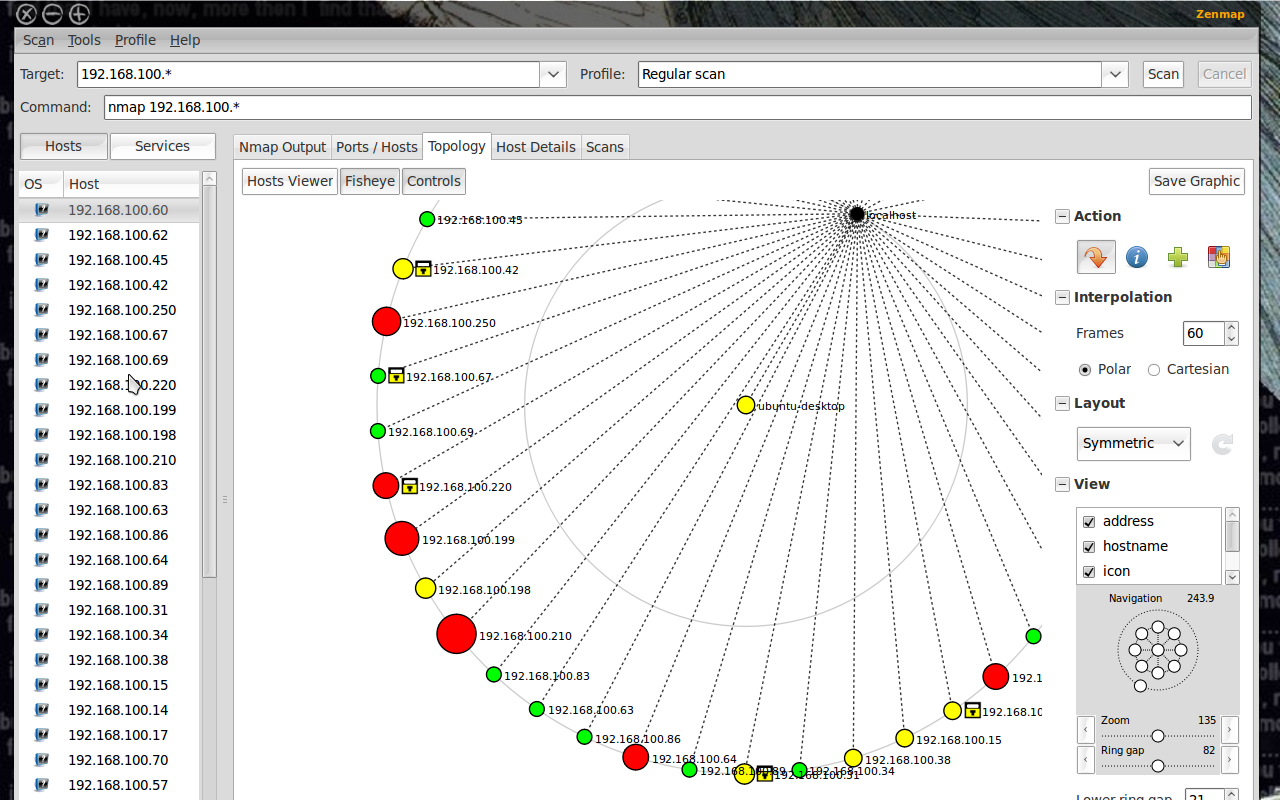
In addition to providing visual network mappings, Zenmap also allows you to save and search your scans for future use.
Zenmap is great for beginners who want to test the capabilities of Nmap without going through a command-line interface.
Nmap Commands Cheat Sheet
Target Specification
|
Switch |
Example |
Description |
|---|---|---|
|
nmap 192.168.1.1 |
Scan a single IP |
|
|
nmap 192.168.1.1 192.168.2.1 |
Scan specific IPs |
|
|
nmap 192.168.1.1-254 |
Scan a range |
|
|
nmap scanme.nmap.org |
Scan a domain |
|
|
nmap 192.168.1.0/24 |
Scan using CIDR notation |
|
|
-iL |
nmap -iL targets.txt |
Scan targets from a file |
|
-iR |
nmap -iR 100 |
Scan 100 random hosts |
|
–exclude |
nmap –exclude 192.168.1.1 |
Exclude listed hosts |
Scan Techniques
|
Switch |
Example |
Description |
|---|---|---|
|
-sS |
nmap 192.168.1.1 -sS |
TCP SYN port scan (Default) |
|
-sT |
nmap 192.168.1.1 -sT |
TCP connect port scan |
|
-sU |
nmap 192.168.1.1 -sU |
UDP port scan |
|
-sA |
nmap 192.168.1.1 -sA |
TCP ACK port scan |
|
-sW |
nmap 192.168.1.1 -sW |
TCP Window port scan |
|
-sM |
nmap 192.168.1.1 -sM |
TCP Maimon port scan |
Host Discovery
|
Switch |
Example |
Description |
|---|---|---|
|
-sL |
nmap 192.168.1.1-3 -sL |
No Scan. List targets only |
|
-sn |
nmap 192.168.1.1/24 -sn |
Disable port scanning. Host discovery only. |
|
-Pn |
nmap 192.168.1.1-5 -Pn |
Disable host discovery. Port scan only. |
|
-PS |
nmap 192.168.1.1-5 -PS22-25,80 |
TCP SYN discovery on port x. Port 80 by default |
|
-PA |
nmap 192.168.1.1-5 -PA22-25,80 |
TCP ACK discovery on port x. Port 80 by default |
|
-PU |
nmap 192.168.1.1-5 -PU53 |
UDP discovery on port x. Port 40125 by default |
|
-PR |
nmap 192.168.1.1-1/24 -PR |
ARP discovery on local network |
|
-n |
nmap 192.168.1.1 -n |
Never do DNS resolution |
Port Specification
|
Switch |
Example |
Description |
|---|---|---|
|
-p |
nmap 192.168.1.1 -p 21 |
Port scan for port x |
|
-p |
nmap 192.168.1.1 -p 21-100 |
Port range |
|
-p |
nmap 192.168.1.1 -p U:53,T:21-25,80 |
Port scan multiple TCP and UDP ports |
|
-p- |
nmap 192.168.1.1 -p- |
Port scan all ports |
|
-p |
nmap 192.168.1.1 -p http,https |
Port scan from service name |
|
-F |
nmap 192.168.1.1 -F |
Fast port scan (100 ports) |
|
–top-ports |
nmap 192.168.1.1 –top-ports 2000 |
Port scan the top x ports |
|
-p-65535 |
nmap 192.168.1.1 -p-65535 |
Leaving off initial port in range |
|
-p0- |
nmap 192.168.1.1 -p0- |
Leaving off end port in range makes the scan go through to port 65535 |
Service and Version Detection
|
Switch |
Example |
Description |
|---|---|---|
|
-sV |
nmap 192.168.1.1 -sV |
Attempts to determine the version of the service running on port |
|
-sV –version-intensity |
nmap 192.168.1.1 -sV –version-intensity 8 |
Intensity level 0 to 9. Higher number increases possibility of correctness |
|
-sV –version-light |
nmap 192.168.1.1 -sV –version-light |
Enable light mode. Lower possibility of correctness. Faster |
|
-sV –version-all |
nmap 192.168.1.1 -sV –version-all |
Enable intensity level 9. Higher possibility of correctness. Slower |
|
-A |
nmap 192.168.1.1 -A |
Enables OS detection, version detection, script scanning, and traceroute |
OS Detection
|
Switch |
Example |
Description |
|---|---|---|
|
-O |
nmap 192.168.1.1 -O |
Remote OS detection using TCP/IP |
|
-O –osscan-limit |
nmap 192.168.1.1 -O –osscan-limit |
If at least one open and one closed |
|
-O –osscan-guess |
nmap 192.168.1.1 -O –osscan-guess |
Makes Nmap guess more aggressively |
|
-O –max-os-tries |
nmap 192.168.1.1 -O –max-os-tries 1 |
Set the maximum number x of OS |
|
-A |
nmap 192.168.1.1 -A |
Enables OS detection, version detection, script scanning, and traceroute |
Timing and Performance
|
Switch |
Example |
Description |
|---|---|---|
|
-T0 |
nmap 192.168.1.1 -T0 |
Paranoid (0) Intrusion Detection |
|
-T1 |
nmap 192.168.1.1 -T1 |
Sneaky (1) Intrusion Detection System |
|
-T2 |
nmap 192.168.1.1 -T2 |
Polite (2) slows down the scan to use |
|
-T3 |
nmap 192.168.1.1 -T3 |
Normal (3) which is default speed |
|
-T4 |
nmap 192.168.1.1 -T4 |
Aggressive (4) speeds scans; assumes |
|
-T5 |
nmap 192.168.1.1 -T5 |
Insane (5) speeds scan; assumes you |
|
Switch |
Example input |
Description |
|---|---|---|
|
–host-timeout <time> |
1s; 4m; 2h |
Give up on target after this long |
|
–min-rtt-timeout/max-rtt-timeout/initial-rtt-timeout <time> |
1s; 4m; 2h |
Specifies probe round trip time |
|
–min-hostgroup/max-hostgroup <size<size> |
50; 1024 |
Parallel host scan group |
|
–min-parallelism/max-parallelism <numprobes> |
10; 1 |
Probe parallelization |
|
–scan-delay/–max-scan-delay <time> |
20ms; 2s; 4m; 5h |
Adjust delay between probes |
|
–max-retries <tries> |
3 |
Specify the maximum number |
|
–min-rate <number> |
100 |
Send packets no slower than <numberr> per second |
|
–max-rate <number> |
100 |
Send packets no faster than <number> per second |
NSE Scripts
|
Switch |
Example |
Description |
|---|---|---|
|
-sC |
nmap 192.168.1.1 -sC |
Scan with default NSE scripts. Considered useful for discovery and safe |
|
–script default |
nmap 192.168.1.1 –script default |
Scan with default NSE scripts. Considered useful for discovery and safe |
|
–script |
nmap 192.168.1.1 –script=banner |
Scan with a single script. Example banner |
|
–script |
nmap 192.168.1.1 –script=http* |
Scan with a wildcard. Example http |
|
–script |
nmap 192.168.1.1 –script=http,banner |
Scan with two scripts. Example http and banner |
|
–script |
nmap 192.168.1.1 –script “not intrusive” |
Scan default, but remove intrusive scripts |
|
–script-args |
nmap –script snmp-sysdescr –script-args snmpcommunity=admin 192.168.1.1 |
NSE script with arguments |
Useful NSE Script Examples
|
Command |
Description |
|---|---|
|
nmap -Pn –script=http-sitemap-generator scanme.nmap.org |
http site map generator |
|
nmap -n -Pn -p 80 –open -sV -vvv –script banner,http-title -iR 1000 |
Fast search for random web servers |
|
nmap -Pn –script=dns-brute domain.com |
Brute forces DNS hostnames guessing subdomains |
|
nmap -n -Pn -vv -O -sV –script smb-enum*,smb-ls,smb-mbenum,smb-os-discovery,smb-s*,smb-vuln*,smbv2* -vv 192.168.1.1 |
Safe SMB scripts to run |
|
nmap –script whois* domain.com |
Whois query |
|
nmap -p80 –script http-unsafe-output-escaping scanme.nmap.org |
Detect cross site scripting vulnerabilities |
|
nmap -p80 –script http-sql-injection scanme.nmap.org |
Check for SQL injections |
Firewall / IDS Evasion and Spoofing
|
Switch |
Example |
Description |
|---|---|---|
|
-f |
nmap 192.168.1.1 -f |
Requested scan (including ping scans) use tiny fragmented IP packets. Harder for packet filters |
|
–mtu |
nmap 192.168.1.1 –mtu 32 |
Set your own offset size |
|
-D |
nmap -D 192.168.1.101,192.168.1.102, |
Send scans from spoofed IPs |
|
-D |
nmap -D decoy-ip1,decoy-ip2,your-own-ip,decoy-ip3,decoy-ip4 remote-host-ip |
Above example explained |
|
-S |
nmap -S www.microsoft.com www.facebook.com |
Scan Facebook from Microsoft (-e eth0 -Pn may be required) |
|
-g |
nmap -g 53 192.168.1.1 |
Use given source port number |
|
–proxies |
nmap –proxies http://192.168.1.1:8080, http://192.168.1.2:8080 192.168.1.1 |
Relay connections through HTTP/SOCKS4 proxies |
|
–data-length |
nmap –data-length 200 192.168.1.1 |
Appends random data to sent packets |
Example IDS Evasion command
nmap -f -t 0 -n -Pn –data-length 200 -D 192.168.1.101,192.168.1.102,192.168.1.103,192.168.1.23 192.168.1.1
Output
|
Switch |
Example |
Description |
|---|---|---|
|
-oN |
nmap 192.168.1.1 -oN normal.file |
Normal output to the file normal.file |
|
-oX |
nmap 192.168.1.1 -oX xml.file |
XML output to the file xml.file |
|
-oG |
nmap 192.168.1.1 -oG grep.file |
Grepable output to the file grep.file |
|
-oA |
nmap 192.168.1.1 -oA results |
Output in the three major formats at once |
|
-oG – |
nmap 192.168.1.1 -oG – |
Grepable output to screen. -oN -, -oX – also usable |
|
–append-output |
nmap 192.168.1.1 -oN file.file –append-output |
Append a scan to a previous scan file |
|
-v |
nmap 192.168.1.1 -v |
Increase the verbosity level (use -vv or more for greater effect) |
|
-d |
nmap 192.168.1.1 -d |
Increase debugging level (use -dd or more for greater effect) |
|
–reason |
nmap 192.168.1.1 –reason |
Display the reason a port is in a particular state, same output as -vv |
|
–open |
nmap 192.168.1.1 –open |
Only show open (or possibly open) ports |
|
–packet-trace |
nmap 192.168.1.1 -T4 –packet-trace |
Show all packets sent and received |
|
–iflist |
nmap –iflist |
Shows the host interfaces and routes |
|
–resume |
nmap –resume results.file |
Resume a scan |
Helpful Nmap Output examples
|
Command |
Description |
|---|---|
|
nmap -p80 -sV -oG – –open 192.168.1.1/24 | grep open |
Scan for web servers and grep to show which IPs are running web servers |
|
nmap -iR 10 -n -oX out.xml | grep “Nmap” | cut -d ” ” -f5 > live-hosts.txt |
Generate a list of the IPs of live hosts |
|
nmap -iR 10 -n -oX out2.xml | grep “Nmap” | cut -d ” ” -f5 >> live-hosts.txt |
Append IP to the list of live hosts |
|
ndiff scanl.xml scan2.xml |
Compare output from nmap using the ndif |
|
xsltproc nmap.xml -o nmap.html |
Convert nmap xml files to html files |
|
grep ” open ” results.nmap | sed -r ‘s/ +/ /g’ | sort | uniq -c | sort -rn | less |
Reverse sorted list of how often ports turn up |
Miscellaneous Options
|
Switch |
Example |
Description |
|---|---|---|
|
-6 |
nmap -6 2607:f0d0:1002:51::4 |
Enable IPv6 scanning |
|
-h |
nmap -h |
nmap help screen |
Other Useful Nmap Commands
|
Command |
Description |
|---|---|
|
nmap -iR 10 -PS22-25,80,113,1050,35000 -v -sn |
Discovery only on ports x, no port scan |
|
nmap 192.168.1.1-1/24 -PR -sn -vv |
Arp discovery only on local network, no port scan |
|
nmap -iR 10 -sn -traceroute |
Traceroute to random targets, no port scan |
|
nmap 192.168.1.1-50 -sL –dns-server 192.168.1.1 |
Query the Internal DNS for hosts, list targets only |
Conclusion
Nmap is clearly the “Swiss Army Knife” of networking, thanks to its inventory of versatile commands.
It lets you quickly scan and discover essential information about your network, hosts, ports, firewalls, and operating systems.
Nmap has numerous settings, flags, and preferences that help system administrators analyze a network in detail.