Digital Forensics, Part 2: Live Memory Acquisition and Analysis
In some cases, the forensic investigator will need to grab an image of the live memory. Remember, RAM is volatile and once the system is turned off, any information in RAM will be likely lost. This information may include passwords, processes running, sockets open, clipboard contents, etc. All of this information must be captured before powering down the system or transporting it. | Digital Forensics

In addition, many hard drives are encrypted with such things as TrueCrypt and the password for these encryption regimes resides in RAM. If the hard drive is encrypted, then capturing volatile data is even more crucial as the hard drive information may be unavailable to the forensic investigator without it.
There are many tools for capturing data from memory, but one company, Access Data, has been providing their FTK (Forensic Tool Kit) Imager for years for free and, as a result, it has become the de-facto standard in image capturing. You can the FTK Imager at Access Data’s website.
Live memory acquisition and analysis, also known as live forensics or hot imaging, is a technique used by forensic investigators to collect and analyze data from a computer or device that is currently powered on and in use. This can be a valuable tool for investigators, as it allows them to gather evidence that might be lost or altered if the device is shut down and restarted.
There are a number of methods that can be used for live memory acquisition, including direct memory access (DMA) and kernel-level acquisition. DMA involves physically connecting to the device’s memory bus and copying the contents of memory directly, while kernel-level acquisition involves using specialized software to access the device’s memory from within the operating system.
Once the live memory of a device has been acquired, it can be analyzed using a variety of tools and techniques. This can include analyzing the device’s running processes, examining the contents of its memory, and searching for specific keywords or patterns.
One of the key benefits of live memory acquisition and analysis is that it allows investigators to gather evidence that might be lost or altered if the device is shut down and restarted. This can be especially important in cases where the device is being used to commit crimes, as shutting it down could destroy evidence or cause the perpetrator to become aware of the investigation.
Live memory acquisition and analysis can also be useful for detecting malware or other malicious activity that might not be detectable through traditional methods. By analyzing the device’s memory in real-time, investigators can identify and analyze malware that is actively running on the device, rather than relying on static analysis of stored files.
There are some limitations to live memory acquisition and analysis, however. It requires specialized equipment and expertise, and it can be time-consuming and resource-intensive. In addition, it may not be possible to acquire live memory from certain types of devices, such as those that are encrypted or have been damaged.
Despite these limitations, live memory acquisition and analysis is an important tool for forensic investigators, and it is likely to continue to be a valuable technique for collecting and analyzing evidence from powered-on devices.
Step 1: Using the FTK Imager to Capture Memory
Once we have downloaded and installed FTK Imager, we should be greeted by a screen like that below.

Next, click on the “File” pull down menu and go to the “Capture Memory” selection.

It will open a window like that below. You will have to select where to store your memory dump, what to call the file, whether you want to include the page file (virtual memory), and whether you want to create an AD1 file (AccessData’s proprietary data type).

In my case, I created a directory called “memory dumps”, named the file memdump.mem, included the virtual memory or pagefile, but did not create an AD1 file. I recommend you do something similar.
When you completed each of these, click the “Capture Memory” button.
This will start a window that will track the progress of your capture. If the system has a lot of memory, that could take awhile.
Step 2: Volatility Memory Analysis Tool
Analyzing a memory capture is a bit different from a hard drive analysis. One of the beauties of memory analysis is the ability to actually recreate what the suspect was doing at the time of the system capture.
Among the most widely used tools for memory analysis is the open-source tool appropriately named Volatility. It is built into Kali Linux, so there’s no need to download it. Simply transfer the memory image you captured to your Kali machine and we can begin our analysis.
If you aren’t using Kali, you can download volatility from www.volatilityfoundation.org. It has been ported for Window, Linux, and Mac OS X, so it will work on nearly any platform.
Step 3: Using Volatility for Analysis
To use Volatility, navigate to /usr/share/volatility
kali > cd /usr/share/volatility
Since Volatility is a python script, you will need to preface the command with the keyword python. To view the help page, type:
kali > python vol.py -h
This will display a long list a command options.


Before we can do any work on this memory image, we first need to get the profile of the image. This will retrieve key information from the image. This profile will then help volatility to determine where in the memory capture key information resides, as each operating system places information in different address spaces.
To get the profile, type:
kali > python vol.py imageinfo -f /location of your imagefile
For instance, I put my image on my desktop, so my command would be:
kali > python vol.py imageinfo -f /root/Desktop/memdump.mem
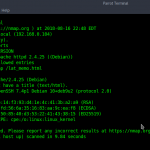
This command will examine the memory file for evidence of the operating system and other key information.

As you can see in the screenshot above, Volatility identified the OS as Win7SP0x64 (Windows 7, no service pack, 64-bit). It also identifies AS layer1 and 2, the number of processors, the service pack, and the physical address space for each processor, among many other things.
Step 4: Using the Profile
Now that we have recovered the profile of this memory dump, we can begin to use some of the other functionality of Volatility. For instance, if we wanted to list the registry hives including SAM, we could use the hiveinfo plugin by typing:
kali > python vol.py –profile Win7SP1x64 hivelist -f /location of your image/

Note that Volatility was able to list all of the hives including their virtual and physical location in RAM.
Parsing out the image profile is crucial, as each operating system stores information in different places in RAM. Volatility needs to know the profile (OS, service pack, and architecture) to know where to look in the memory image for the necessary information. If you put in the wrong profile information, Volatility will throw errors telling you it can’t parse the information properly. In that case, try another image profile. Unfortunately, the profile image that this tool provides is not always correct.
Step 5: Getting the List of Processes
As our next step, let’s see if we can find the processes that the suspect had running when we captured the RAM image. We can do this by typing:
kali > python vol.py –profile Win7SP1x64 pslist -f /root/Desktop/memdump.mem

Let’s break that down:
-
python is the interpreter.
-
vol.py is the name of the Volatility script.
-
–profile Win7SP1x64 is the profile of the system the memory image was captured from.
-
pslist is the plugin to parse out the running processes.
-
-f /root/Desktop/memdump.mem is the location of the image file.

As you can see, Volatility has parsed out all the running processes. To gather even more information from the RAM image, we can use exactly the same command as above with the exception of changing the name of the plugin.
To get a list of available plugins you could use, type:
kali > python vol.py -h

Step 6: Getting the Running DLLs
To view the running DLLs on the system, we simply use the dlllist plugin like below:
kali > python vol.py –profile Win7SP1x64 dlllist -f /root/Desktop/memdump.mem

As you can see, Volatility parsed out a list of all the running DLLs.
Step 7: Getting the Contents of the System’s Clipboard
Sometimes, what the suspect had in their clipboard can be incriminating. We can retrieve the information from the suspect’s RAM by using the clipboard plugin like below.
kali > python vol.py –profile Win7SP1x64 clipboard -f /root/Desktop/memdump.mem

Unfortunately, all this information is in hexadecimal and must be translated to ASCII.
Step 8: Getting a Timeline of Events
Often times, to prove that a suspect actually committed the action they are accused of, we may need a timeline of events that took place on that system. We can retrieve this timeline information from the memory image by using the timeliner plugin like below.
kali > python vol.py –profile Win7SP1x64 timeliner -f /root/Desktop/memdump.mem

Note that each process is time stamped.
Step 9: Looking for Malware in the Memory
Lastly, let’s look for any malware running in the memory of the suspect system. Volatility has a plugin especially designed for this purpose, appropriately named malfind. We can use it like any other Volatility plugin. Simply type the same command as above but replace the name of the plugin with malfind.
kali > python vol.py –profile Win7SP1x64 malfind -f /root/Desktop/memdump.mem

Volatility is a powerful memory analysis tool with tens of plugins that enable us to find evidence of what the suspect was doing at the time of computer seizure